- Key Takeaways on Google Search Console Security Issues
- Understanding Google Search Console Security Issues
- Identifying Google Search Console Security Issues and Concerns
- Assessing Security Problems
- Fixing Google Search Console Security Issues
- Best Practices for Website Security
- Requesting a Review for Security Issues
- Getting Support for Search Console Security Concerns
- Managing Social Engineering Violations
- In Summary Google Search Console Security Issues
- FAQs on Google Search Console Security Issues
Key Takeaways on Google Search Console Security Issues
- Understanding Security Issues
- Recognize the importance of being vigilant about security threats to your website.
- Identifying Security Concerns
- Regularly monitor your Google Search Console for any security alerts or notifications.
- Assessing Security Problems
- Investigate any reported security issues promptly to understand the extent of the problem.
- Fixing Security Issues
- Take immediate action to address and resolve any security vulnerabilities detected on your website.
- Best Practices for Website Security
- Implement robust security measures such as using strong passwords, keeping software updated, and enabling HTTPS encryption.
- Requesting a Review for Security Issues
- Follow the necessary steps to request a review from Google once you have fixed the security issues on your website.
Google Search Console is a powerful tool for website owners, but it’s crucial to be aware of potential security issues that could compromise your site from hackers. Navigating and addressing security problems can safeguard your online presence. By staying informed and proactive, you can protect your website from cyber threats with a security review and maintain its integrity. Let’s delve into the realm of Google Search Console security issues to equip site owners and web users with the knowledge needed to fortify their digital domain.
View the details of the full post @googlewmc
Understanding Google Search Console Security Issues
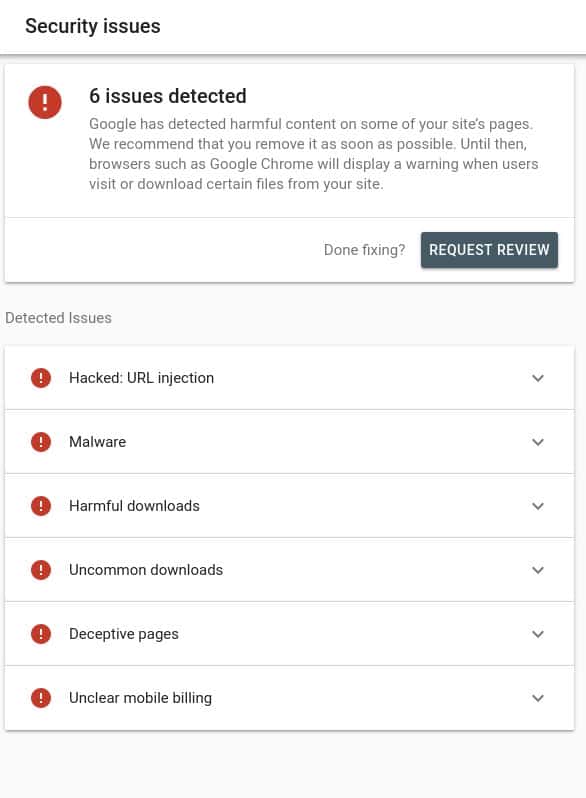
Types of Google Search Console Security Issues
Different types of security issues, such as changes, can impact your website’s performance in Google Search Console. It is crucial to understand these various types, of security issues report, to ensure a secure online presence. By identifying and addressing specific security issues and making changes, you can protect your website from potential threats effectively. Common types include malware infections, phishing attacks, hacked content, and social engineering.
They can harm both your website and its visitors by spreading malicious software. Phishing attacks, a form of social engineering, aim to steal sensitive information through deceptive means like fake login pages. Hacked content involves unauthorized access that alters the appearance or functionality of your site without permission.
Hacked Accounts
If you suspect that your Google Search Console account has been hacked, immediate action is necessary as it could lead to unauthorized control over your website. Recovering a hacked account involves following specific steps provided by Google to regain control promptly. Regularly monitoring for unusual activities and enabling two-factor authentication are essential preventive measures against hacking attempts.
Unauthorized Requests
Suspicious activity on your website may be indicated by unauthorized requests, which could potentially compromise its integrity. Monitoring and identifying such requests are vital for maintaining a secure online environment and addressing security issues. Taking necessary actions like blocking suspicious IP addresses or implementing firewalls helps prevent security breaches effectively.
Harmful Downloads
Harmful downloads pose a significant threat not only to users but also to the reputation of your website. Regularly scanning for harmful downloads and pages is crucial in ensuring a safe browsing experience for visitors while protecting their devices from malware infections or unwanted software installations.
Deceptive Content
Regularly reviewing pages and identifying deceptive content is essential for maintaining a positive user experience online. Removing or modifying deceptive content on pages promptly protects the integrity of your site while preserving user trust in the long run.
Embedded Content
Improperly managed embedded content on pages can introduce security vulnerabilities into websites if left unchecked; therefore, regular audits help ensure adherence to security best practices. Addressing any identified security concerns related to embedded content on pages safeguards websites against potential threats effectively.
Identifying Google Search Console Security Issues and Concerns
Diagnosing Malware
Malware diagnosis involves spotting and analyzing harmful software on your website. Special tools and methods can help detect malware effectively. Addressing diagnosed malware promptly is essential to prevent further harm to your site’s security.
Regularly scanning for malware ensures that any infections are caught early, preventing potential damage. Tools like Google Search Console provide alerts if malicious content is detected on pages, aiding in swift removal.
Crawling Issues
Crawling problems may block search engine bots from accessing and indexing your website pages. Detecting and fixing these issues guarantees that search engines properly index your site’s content. Consistent monitoring helps ensure optimal visibility in search results.
If crawling errors persist, it could lead to decreased organic traffic as search engines struggle to access or understand the content on the website.
Unnatural Links
Unnatural links can harm your website’s ranking and credibility. Regular link audits help identify and remove spammy or unnatural links on pages efficiently. Taking action, such as disavowing these links, maintains a healthy backlink profile.
Search engines penalize websites with unnatural links by lowering their rankings in search results; thus, it’s crucial to regularly audit backlinks.
Deceptive Ads
Deceptive ads mislead users and compromise online safety. Monitoring ads regularly ensures compliance with advertising policies while removing deceptive ads promptly protects user trust for a secure browsing experience.
Misleading advertisements not only harm user experience but also violate ethical standards set by various platforms.
Assessing Security Problems
Manual Actions vs Google Search Console Security Issues
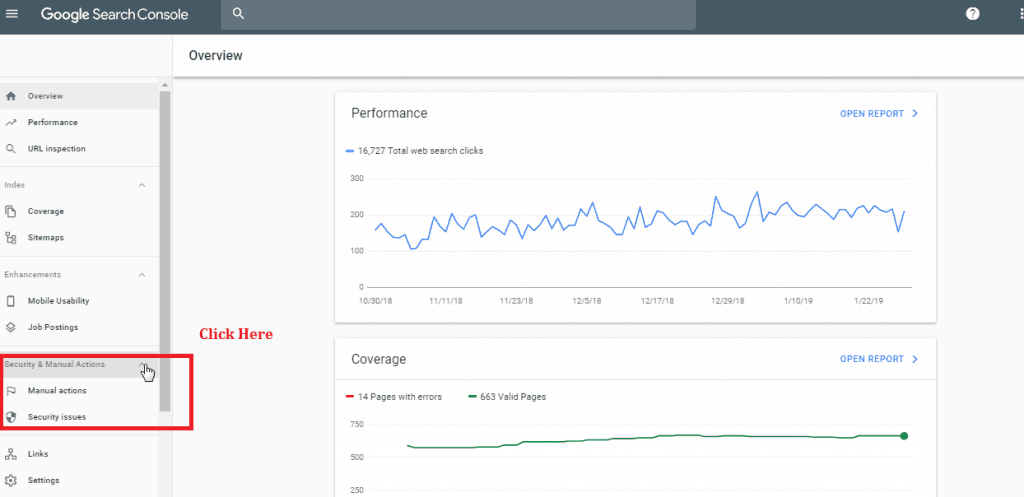
Understanding the difference between manual actions and issues is crucial for managing Google Search Console security concerns effectively. Manual actions are penalties given by Google for guideline violations, while issues indicate potential security risks. Resolving manual actions involves adhering to Google’s guidelines, whereas addressing issues requires identifying and mitigating security threats promptly.
Confirming problems entails verifying the presence of security issues on your website. By utilizing tools within Google Search Console, you can confirm identified problems accurately. This confirmation enables you to take necessary steps to address these security vulnerabilities effectively and prevent any potential harm to your website.
Utilizing Tools
Verification Process
The verification process ensures that you have control or ownership over the website under scrutiny. Following Google Search Console’s specific verification steps is vital in gaining access to essential security features provided by the platform. Successfully completing this process grants you the capability to monitor and resolve any detected security breaches promptly.
Google Search Console Security Issues Reports
Security reports offer valuable insights into potential threats detected on your website, helping you stay informed about its overall security status. Regularly reviewing these reports allows you to proactively address any emerging security risks, maintaining a secure online presence consistently.
Fixing Google Search Console Security Issues
Removing Malicious Code
Removing malicious code is vital to eliminate security vulnerabilities on your website. Conduct thorough scans and audits to detect and remove any malicious code present. Update and secure your website’s code regularly to prevent future infections effectively.
Addressing hacking involves dealing with unexpected changes in your website’s appearance or functionality, which could signal a security breach. Timely investigation and resolution of these changes are crucial to reduce potential risks. Regular monitoring helps identify and correct any unauthorized alterations swiftly.
Unexpected Changes
Unexpected alterations in how your website looks or operates may indicate a security breach has occurred. It is essential to promptly investigate and address these changes to mitigate potential risks effectively. Consistent monitoring aids in identifying and rectifying any unauthorized modifications made to your site without delay.
Fixing Vulnerabilities
Fixing vulnerabilities requires patching up security loopholes that attackers could exploit easily. Regularly updating software, plugins, themes can help address known vulnerabilities efficiently. Enhancing website protection by employing additional security measures like implementing a web application firewall further strengthens the site’s defense against cyber threats.
Addressing outbound links ensures they do not direct users towards malicious or harmful websites, maintaining a safe browsing experience for visitors consistently. Regularly reviewing and validating outbound links is key to upholding a secure online environment for users navigating through your site safely. Prompt removal or disavowal of suspicious outbound links safeguards the reputation of your website from potential harm.
Best Practices for Website Security
Following Guidelines
Adhering to Google’s guidelines is paramount in maintaining a secure website through the Search Console. Compliance with these guidelines ensures adherence to best practices, reducing the risk of penalties and security issues. Staying updated with Google’s recommendations by regularly reviewing them can safeguard your website’s performance effectively.
Regularly conducting security audits plays a crucial role in identifying and addressing potential risks on your website proactively. By implementing robust security measures like strong passwords and two-factor authentication, you can significantly reduce the likelihood of future security threats. Removing risks involves taking proactive steps towards eliminating any vulnerabilities that could compromise your website’s security.
Removing Risks
Regular updates of software, plugins, themes, and content management systems are essential components for ensuring website security. Keeping all these elements up to date helps in addressing known vulnerabilities promptly while ensuring optimal performance for your site. By regularly checking for updates and applying them promptly, you minimize the chances of experiencing security breaches that could harm your website or compromise user data.
Updating regularly is not just about new features; it also addresses critical bug fixes that enhance overall website stability while boosting its resilience against potential cyber threats. Regularly updating various aspects of your site demonstrates diligence in protecting both web users’ information as well as safeguarding the integrity of web pages from malicious attacks.
Requesting a Review for Security Issues
Review Process
Regular reviews of your website’s compliance with Google’s guidelines and security standards are crucial. These reviews help catch any potential violations or security issues, ensuring ongoing adherence to the rules. By addressing these problems promptly, you maintain a secure online environment for your users.
Conducting routine checks also demonstrates your commitment to maintaining a safe platform. For instance, if an unauthorized user gains access to sensitive data on your site, regular reviews can help identify and rectify such breaches swiftly. This proactive approach safeguards both your website and its visitors from potential harm.
Submitting Requests
When encountering specific security concerns beyond your expertise, submitting requests to Google is essential. By following the proper channels and procedures when reaching out for assistance, you ensure that your inquiries receive prompt attention. Whether it’s resolving intricate security issues or seeking clarification on certain matters, submitting requests can provide the necessary support.
For example, suppose you suspect that malware has infected your website but lack the technical knowledge to address it effectively. In that case, submitting a request through Google Search Console can connect you with experts who can guide you through the process of removing malicious code from your site.
Getting Support for Search Console Security Concerns
Google Support Channels
When facing Google Search Console security issues, reaching out to the support team through official channels like email or live chat is crucial. Utilizing these channels ensures timely assistance in addressing any security-related inquiries or challenges you encounter with your website. Google’s support system is designed to provide guidance and solutions tailored to your specific security concerns, offering a direct line of communication with experts who can help navigate and resolve issues effectively.
Engaging with the host via Google’s support channels allows you to tap into a wealth of knowledge and expertise dedicated to ensuring the security of your website. Whether you suspect unauthorized access, malware infections, or other potential threats, contacting Google support enables you to receive prompt assistance in safeguarding your online platform from vulnerabilities that could compromise its integrity.
Community Forums Support for Google Search Console Security Issues
Apart from seeking help directly from Google’s support team, participating in community forums offers another avenue for addressing Google Search Console security issues collaboratively. By joining discussions on these platforms, webmasters can share experiences and insights related to resolving various security challenges they may face. The collective wisdom shared on community forums contributes significantly to fostering a supportive environment where individuals can learn from each other’s encounters with website security threats.
Community forums serve as valuable spaces where webmasters can seek advice, exchange tips, and explore different approaches towards enhancing their websites’ defenses against potential cyber threats. Leveraging the power of communal knowledge not only helps in identifying and mitigating existing vulnerabilities but also aids in implementing proactive measures that fortify your website’s overall security posture.
Managing Social Engineering Violations
Recognizing Violations
Recognizing Google Search Console security issues involves identifying instances where your website doesn’t meet Google’s guidelines. By understanding these violations, you can take the necessary steps to correct them. Regularly checking for potential violations is crucial to ensure your website complies with Google’s standards.
To recognize violations, pay attention to any suspicious activities on your site that could indicate security breaches. For instance, if you notice unauthorized changes or unfamiliar content appearing on your web pages, it might signal a violation. Sudden drops in search engine rankings or warnings from Google about potential issues should prompt immediate investigation.
- Unauthorized changes on the website
- Unfamiliar content added without permission
- Sudden decreases in search engine rankings
Resolving Violations
Resolving Google Search Console security concerns requires implementing corrective actions to address non-compliance with Google’s guidelines promptly. Following the recommended steps provided by Google is essential for effectively resolving these violations and ensuring your website maintains compliance with their standards.
When addressing violations, act swiftly to rectify any identified issues and vulnerabilities on your website. This proactive approach not only helps safeguard your site but also fosters a positive relationship with search engines like Google. By promptly fixing security problems and adhering to best practices outlined by Google, you demonstrate a commitment to maintaining a secure online environment for users.
- Promptly rectify identified issues.
- Follow step-by-step guidance from Google.
- Demonstrate commitment to maintaining a secure online environment.
In Summary Google Search Console Security Issues
You’ve now grasped the essentials of handling security issues on your website. Identifying, assessing, and fixing problems is crucial. Remember to implement best practices, request reviews, and seek support promptly. Managing social engineering violations demands vigilance. Stay proactive to safeguard your online presence effectively.
In a world where digital threats lurk around every corner, taking charge of your website’s security is non-negotiable. By following the steps outlined here, you’re arming yourself with the knowledge needed to combat potential breaches. Your website’s safety is in your hands – act wisely.
